Looking at Network Connections on IBM i with NETSTAT
If you’re running web applications, database servers, FTP, SSH, or other network programs, the IBM i NETSTAT command can tell you what is connecting to your system, which ports are in use, which programs are listening for network connections, and more.
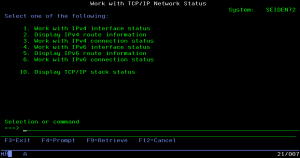
When you run NETSTAT from a 5250 command line, the main screen provides options for interface status (network addresses and lines), routes (how it forwards traffic outside of the local network), and connections. We’re interested in the connection status option, which includes programs listening for new connections as well as ongoing connections. A shortcut to the connection status screen is NETSTAT *CNN.
Screens for both IPv4 and IPv6 are offered. IPv6 is the successor to IPv4, but not everyone has migrated to IPv6 yet. In this article, we’ll show using IPv4, but the principles apply to both.
Looking at connections
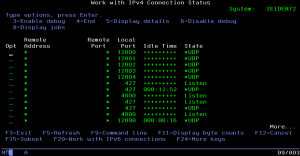
In the screen for connection status, you’ll see different kinds of sockets that represent current or future connections. All sockets on your system have port numbers that they communicate over. The listening system will listen on a specifically configured port number, while outgoing ports will have a random port number assigned to them. This means that sockets on your system that are listening will show their assigned port number locally, while connections that your system makes to other systems will have the port number assigned on the remote end. Names of services are shown when available; you can press F14 to show the port numbers instead.
The default view displays the state of the connection:
- Listen means that this socket is listening for new connections.
- Established are ongoing connections. Each established connection has a remote address (corresponding to the other end).
- Closed means the connection is going away.
- Before a connection becomes established or closed, it has to go through a handshake. This involves sending SYN, ACK, and FIN in either direction. You’ll see these when a connection starts or stops.
- UDP means that the socket is connectionless, meaning the socket simply receives and sends messages without having to establish a connection. This is faster, but not as reliable. (The other kind of connection is TCP, which uses connections and handles network problems at the protocol level, but is not as fast.)
Idle time is displayed for connections that have had activity at one point.
Additional screens
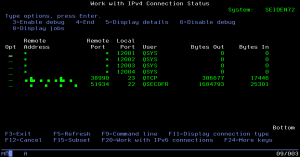
Every socket is owned by a user. You can press F11 to see who owns each socket. In addition, you can see how many bytes have been transfered over the socket in each direction.
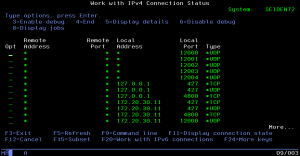
If you press F11 again, you can see what protocol (the layer 4 kind) the socket is using (either the connection-based reliable TCP, or the connectionless fast UDP), and the local address of the socket. A wildcard means that the socket will listen on all addresses, whereas a specific IP means the socket only listens on that IP. Note that loopback IPs (anything beginning with 127 on IPv4, or ::1 on IPv6) are only accessible from the same computer.
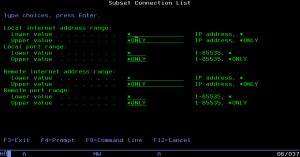
Want to see only specific IP or port ranges? Just hit F15, and enter a range you want to see for the local and remote ends.
What’s talking? How long?
On each connection, two different options can show you more about a socket.
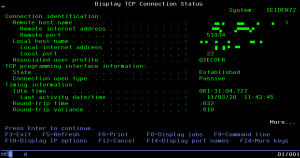
The first is option 5, “Display details”. This displays a lot of gory details about the socket, primarily useful for networking engineers. For example, timing information is useful for determining latency and activity.
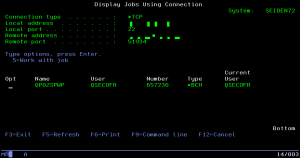
The second is option 8, “Display jobs”. This displays what jobs are associated with the socket, and a further option 5 on the job will show the familar “Work with Job” screen you can get to from WRKACTJOB. Some sockets don’t belong to any jobs, but belong to the IBM i kernel. If so, this screen will show tasks using the connection instead.
What can I do with this?
Need to assign a port to a web server, but don’t know which ports are free? Just look through the connection status, and see what sockets are listening. If you need to reassign a port number, then you can easily find out what job is using it, and reconfigure that specific job.
Starting a program, but curious what it listens on? Or if it’s even listening at all? Just start it and see if new sockets appear in the list.
Curious about what SSH connections are open on your system? Systems exposed to the internet will tend to have many attempts at an SSH connection; they’ll be short lived as they fail authentication. As you refresh, you can watch as the TCP connection is negotiated, SSH authentication is briefly attempted, and the connections wither away. If a connection stays open, you can see where it originated (including reverse DNS in option 5) and how much has been transfered over it.
Every admin should be able to determine what is going on in their system; with NETSTAT, asking who and what about a connection is much easier.

Leave a Reply
Want to join the discussion?Feel free to contribute!